On Wednesday December 17th, episode 4 of the TV show SCAM ALERT (RTL5, available on Videoland, paywalled) covered an Incident Response case I was involved in back in late 2021. Personal details of the victim were shown, including screenshots of a payment to Farfetch for a watch.
Now that the case has become this public, in good consultation with Christ himself, I thought it would be interesting to dig a bit deeper into the technical context in a blog post.
So here it is, four years later: a post-mortem of what actually happened.
The report: "My money is gone"
On December 30, 2021, I got a phone call about a fraud case.
Christ had been called the evening before by someone pretending to be a bank employee. During that call, he was convinced to install AnyDesk so the caller could "have a look together." He described that during the session, his screen went black multiple times.
Afterwards, roughly €21,000 had vanished from his account.
The obvious assumption was:
- computer taken over
- online banking accessed
- money siphoned off
We assumed the money was gone for good, but the use of AnyDesk made the case interesting enough to take a closer look at the computer.
Don't touch anything first
Because a police report had been filed, we advised Christ not to touch his computer for now. If the police wanted to do forensic analysis, the system state needed to stay intact.
Later that day, the police confirmed: the computer would not be examined.
That gave us room to investigate ourselves. Christ had already contacted Rabobank, reported the fraud, and they had blocked his debit card — which meant access to his online banking was not possible. So we had to work with whatever logging was on his computer.
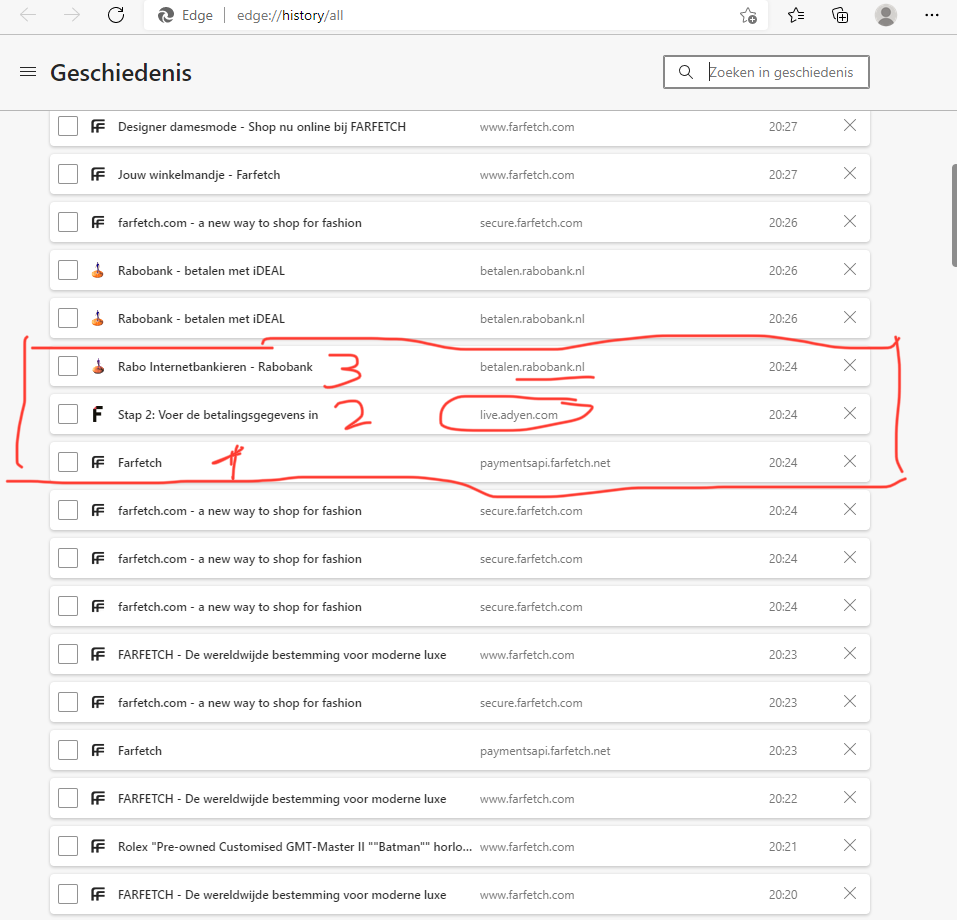
Browser history doesn't lie
By this point Christ's memory had sharpened a bit and he recalled that the scammer had instructed him to google AnyDesk and download it. He had initially mentioned something about a fake Rabobank website, but that turned out not to be the case. It goes to show that victim recollections aren't 100% reliable — not deliberately, but subconsciously — and that technical validation really does matter.
Through a remote session (I did find it amusing to use TeamViewer for that) I secured the browser history from Microsoft Edge. What stood out was that during the AnyDesk session timeframe, there were visits to farfetch.com logged. I didn't know the site, but a quick look made it clear it sells luxury second-hand goods.
The chronology went something like this:
1. Visit to a Rolex product page on farfetch.com
2. Shopping cart
3. Checkout
4. Payment step via paymentsapi.farfetch.net
5. Redirect to betalen.rabobank.nl (iDEAL)
6. Processing via live.adyen.com
All of this happened within a few minutes, around 20:24.
At that point I thought I had found a puzzle piece, but I was still looking for the actual break-in to online banking. Purely based on assumption, I was completely convinced the attacker must have had access to the account and simply transferred money to their own IBAN. I decided to copy the browser history to my own machine and continue the next day.
Realization: no bank access, just iDEAL
The next day it suddenly hit me: what if you can pay €21k through iDEAL? I don't do that every day, and I was so fixated on the attacker having accessed online banking that it hadn't even crossed my mind. But when I checked and found that iDEAL does allow limits that high, I realized that single Farfetch purchase might be the whole story.
This opened up options, because Farfetch, Rabobank, and Adyen are all legitimate companies with reputations to maintain and fraud departments. It was now the 31st and I figured urgency was needed with New Year's Eve approaching, so I reached out to Farfetch and Rabobank on Christ's behalf.
I reached out via email, phone, and social media and shared the transaction details with all three parties.
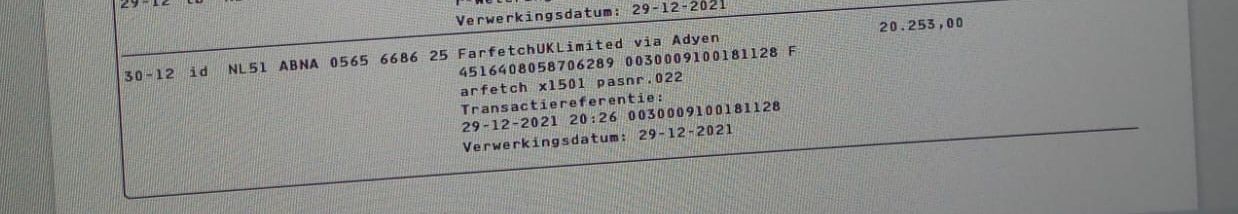
I shared the transaction ID (0030009100181128) and other transaction details with Farfetch. With Rabobank and Adyen, I shared the unique identifiers I could extract from the browser logs of visits to their systems.
`
Farfetch payment initiation: https://paymentsapi.farfetch.net/v1/payments/10000/intents/2868d5ff-7006-422c-a66d-ef1c5eb762d9/charges/7f1a16de-2770-49eb-9baf-7610606d6d4a/instruments/65fd8c26-bd44-4fe5-8581-059e873b8665/redirect?hash=C6PIlE8%2b0u%2f7tsH%2fvFoUJ5Q1vPY7WRBenxNZKaK9A8k%3d
iDEAL landing page: https://betalen.rabobank.nl/ideal-betaling/landingpage?random=d31547fb53b1946f7ca75972e7dfe289f6f77821146204c450ba9b04d101f216&trxid=0030009100181128
Adyen processing: https://live.adyen.com/hpp/completeIdeal.shtml?s=ZqcyU9ZuFlMIJXT94JnTff9ToaDpeUbQogCTNNxGruc%3D&pspEchoData=4516408058706289%3A2025300%3A0021%3A399893%3A6YGBgx07evHgXWdC2ancienSTl4%3D&trxid=0030009100181128&ec=4516408058706289
`
I was hoping the payment chain could help pressure Farfetch. We didn't know Farfetch, so we weren't sure if or how quickly they'd respond to our request.
Whether that pressure helped, I don't know. But the fact is that on January 4th we received word that the order would be cancelled and the money refunded! Fantastic news for Christ.
That same day Christ received his new debit card and was able to confirm the money had actually been returned to his account. Zero damage, despite all the worry.
Suspect identification
I had also asked Farfetch for more details about the order, especially the shipping address — hoping to give the police additional information for identifying the perpetrator. Understandably, Farfetch wouldn't share those details with me due to privacy. But they did indicate they would provide that data to the police directly if law enforcement formally requested it.
I did have other information that could help with identification, though. We had also retrieved the AnyDesk logs from Christ's computer. These turned out to contain precise information about when and from where the remote session was initiated. We had the attacker's IP address.
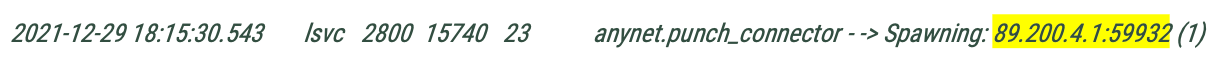
This IP address was in a KPN range for mobile internet. A 4G connection. We had heard through the grapevine that the port behind the IP (59932) could enable KPN to trace it back to an identity.
With these concrete leads (the IP address and Farfetch's offer to cooperate further), I figured there was enough for the police to investigate. I wrote up a statement with everything we had found and submitted it alongside Christ's police report. Whether anything was done with that information, I don't know. The downside in this case is that there was effectively no financial damage anymore, since the money had been returned. That probably didn't help in getting the case prioritized for further investigation.
Conclusion
So in summary, here's how it all played out.
This is how the attacker operated:
- Black out the screen multiple times during the AnyDesk session
- Meanwhile browse through a web shop themselves
- Make Christ believe the iDEAL prompt was a "security check"
The only thing Christ actually saw was the iDEAL screen from his own bank — and he confirmed it.
Technically speaking:
- no malware
- no credential theft
- no bank fraud
Just pure social engineering, with the browser as the weapon. Highly effective.